
In the intricate world of microcontrollers, engineers often find themselves navigating a complex labyrinth of hardware and software hurdles. Like skilled explorers, they must overcome design constraints, optimize performance, and address security vulnerabilities to ensure successful integration.
This article delves into the challenges faced by professionals in this field, providing technical insights and best practices for conquering these obstacles.
By understanding the limitations and complexities involved, readers will gain the knowledge needed to navigate the intricate landscape of microcontroller development with confidence and finesse.
Key Takeaways
- Developers must optimize code for efficient memory usage and select appropriate microcontrollers based on processing speed, memory capacity, and communication interfaces.
- Clever programming techniques like interrupt-driven programming and low-level programming languages enhance microcontroller efficiency and control over hardware peripherals.
- Careful planning, testing, and debugging techniques are crucial for overcoming hardware and software challenges.
- Addressing security vulnerabilities through input validation, secure coding practices, encryption algorithms, and regular firmware updates is essential for maintaining system security.
Understanding Hardware Limitations
Understanding and effectively addressing the hardware limitations associated with microcontrollers is crucial for overcoming challenges in navigating both the hardware and software aspects of these devices.
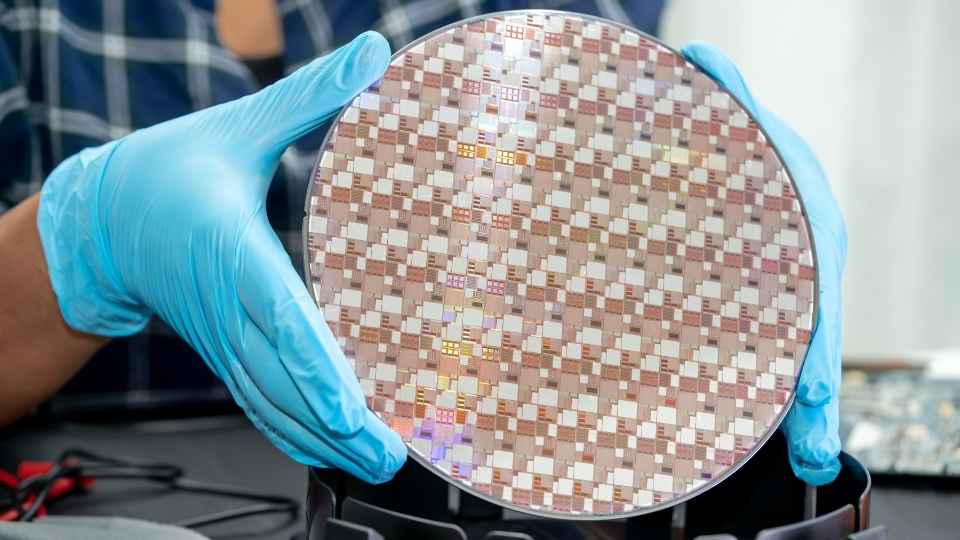
Microcontrollers are designed to be small, low-power devices with limited computational capabilities. This means that they have a restricted amount of memory, processing power, and input/output pins compared to more powerful computing platforms. These limitations can pose significant hurdles when developing complex applications or interfacing with external sensors and peripherals.
To tackle these challenges, developers must carefully optimize their code for efficient memory usage and prioritize critical tasks. They need to select appropriate microcontrollers that meet the requirements of their specific application while considering factors such as processing speed, memory capacity, and available communication interfaces.
Additionally, utilizing clever programming techniques like interrupt-driven programming can help maximize the efficiency of microcontroller resources.
Navigating Software Complexities
Mastering the intricacies of software development for microcontrollers requires a comprehensive grasp of the underlying complexities. As developers strive to bring their ideas to life, they must navigate through various challenges that come with writing code for these tiny computing devices.
One key aspect is memory management, where efficient utilization of limited resources becomes crucial. It involves optimizing code size and ensuring that the program fits within the available memory space.
Additionally, understanding and utilizing low-level programming languages such as assembly or C can greatly enhance control over hardware peripherals and optimize performance.
Debugging also poses unique challenges in this realm due to limited visibility into system states. However, with careful planning and meticulous testing, developers can overcome these hurdles and create robust software solutions for microcontrollers.
Transitioning now to overcoming design constraints...
Overcoming Design Constraints
To successfully develop software for microcontrollers, developers must find innovative solutions to overcome the limitations imposed by design constraints. These constraints can include limited memory, processing power, and I/O capabilities.
One common approach is to optimize code size and execution speed by using efficient algorithms and data structures. Additionally, developers may employ techniques such as code profiling and optimization to identify and eliminate bottlenecks in performance.
Another challenge is interfacing with external devices or sensors that have different voltage levels or communication protocols. Developers can address this by using level shifters or protocol converters to ensure compatibility between the microcontroller and external components.
Furthermore, designing modular software architectures can facilitate code reuse and enable flexibility in adapting to changing requirements.
Strategies for Optimization
Efficiently optimizing code size and execution speed through the utilization of efficient algorithms, data structures, and performance profiling is a key strategy for overcoming the limitations imposed by design constraints in developing software for microcontrollers.
By implementing these strategies, developers can ensure that their software operates within the limited resources available on microcontrollers while maximizing performance.
Some strategies to achieve optimization include:
Utilizing optimized algorithms: Choosing algorithms that have been specifically designed to be efficient in terms of both time and space complexity.
Employing compact data structures: Selecting data structures that minimize memory usage while still providing the necessary functionality.

Profiling code performance: Identifying bottlenecks and areas of improvement through performance profiling tools.
Removing unnecessary operations: Eliminating redundant or unused code to reduce execution time and optimize memory usage.
Leveraging hardware features: Taking advantage of specific features provided by the microcontroller's hardware architecture to improve efficiency.
Addressing Security Vulnerabilities
Addressing security vulnerabilities in software development is crucial for ensuring the protection of sensitive information and preventing unauthorized access or data breaches. In the context of microcontroller-based systems, it becomes imperative to implement robust security measures due to their increasing prevalence in various applications.
One common vulnerability is insufficient validation of user inputs, which can lead to buffer overflow attacks or injection attacks. Implementing input validation techniques such as data sanitization and proper bounds checking can mitigate these risks. Additionally, secure coding practices, such as using encryption algorithms for data transmission and storage, can safeguard against eavesdropping or tampering attempts. Regularly updating firmware and applying patches for known vulnerabilities is also vital.
By addressing security vulnerabilities proactively, developers can create more reliable and trustworthy systems that protect user privacy and maintain the integrity of the overall system architecture.
Transition: While addressing security vulnerabilities is vital for software development, it's equally important to consider best practices for hardware and software integration in microcontroller-based systems.

Best Practices for Hardware and Software Integration
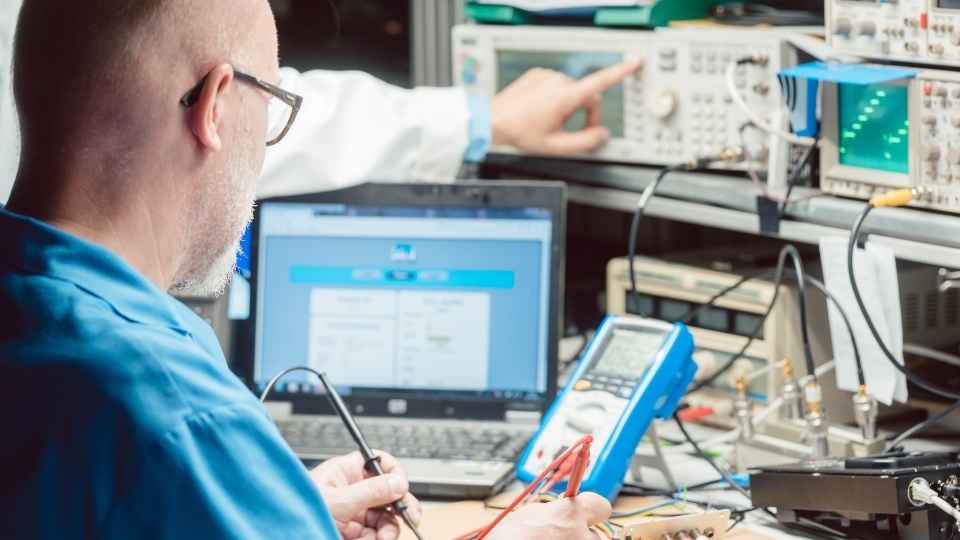
To achieve seamless integration between hardware and software components, it is crucial to follow best practices that ensure synchronization, compatibility, and error handling.
Synchronization between components involves establishing proper communication protocols and timing mechanisms to ensure data consistency and avoid conflicts.
Compatibility with peripherals entails selecting compatible hardware devices and drivers that can seamlessly interact with the software system.
Lastly, implementing effective error handling strategies helps detect and handle potential issues in the integration process, minimizing system failures and ensuring smooth operation.
Synchronization Between Components
A crucial aspect of microcontroller development is achieving proper synchronization between different components. This ensures that all parts of the system work together seamlessly and efficiently. Here are some key considerations for achieving synchronization:
Clock signals: It is important to ensure that all components in the microcontroller system are operating at the same clock frequency. This allows for proper timing and coordination of actions.
Interrupts: Using interrupts allows components to communicate with each other in a timely manner. By interrupting the normal program flow, critical tasks can be handled immediately, improving overall system performance.
Bus protocols: Properly implementing bus protocols such as I2C or SPI enables efficient communication between different components on the microcontroller.
Real-time operating systems (RTOS): RTOS provides multitasking capabilities, allowing multiple tasks to run concurrently while ensuring synchronization between them.
Synchronization primitives: Using techniques like semaphores or mutexes helps manage shared resources and prevent conflicts when multiple components access them simultaneously.
Compatibility With Peripherals
Ensuring seamless compatibility between the microcontroller and its peripherals is crucial for achieving optimal performance and functionality in a system. Peripherals such as sensors, actuators, and communication modules play a vital role in expanding the capabilities of a microcontroller-based system. However, integrating these peripherals with the microcontroller can pose several challenges.
Compatibility between the microcontroller and peripherals involves matching their electrical characteristics, signaling protocols, and software interfaces. It requires careful consideration of voltage levels, data transfer rates, pin configurations, interrupt handling mechanisms, and memory requirements. Additionally, ensuring compatibility also involves selecting peripherals that are supported by the microcontroller's development tools and libraries.
To overcome compatibility challenges, manufacturers provide detailed documentation outlining recommended peripheral options and configurations for specific microcontrollers. This information helps developers make informed decisions when choosing peripherals to ensure seamless integration with the microcontroller.
Error Handling Strategies
One effective strategy for handling errors in microcontroller-based systems is to implement a robust error detection and correction mechanism. This ensures that any errors occurring during the operation of the system are detected and corrected, improving the overall reliability and performance.

There are several strategies that can be employed to achieve this:
Implementing checksums: By adding a checksum value to data packets, it is possible to detect any errors introduced during transmission or storage.
Using redundancy techniques: Redundancy can be added through techniques such as triple modular redundancy (TMR) or voting logic, where multiple copies of critical components are used.
Error-correcting codes: These codes add extra bits to data packets, allowing for the detection and correction of single-bit errors.
Watchdog timers: These timers monitor the system's execution time and reset it if it exceeds a predefined threshold, helping recover from potential software glitches.
Error logging: Storing error information in non-volatile memory allows for post-analysis and debugging of system failures.
Troubleshooting Common Microcontroller Challenges
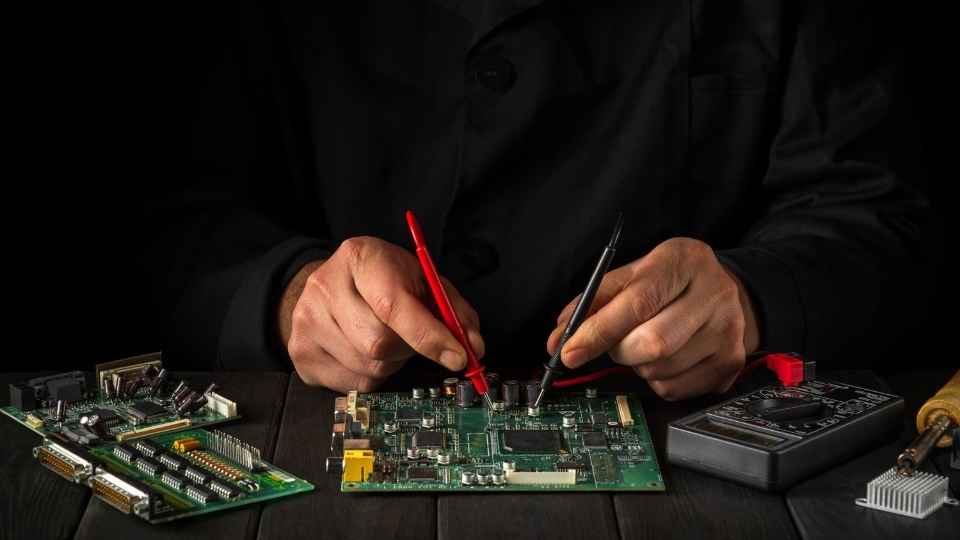
To effectively troubleshoot common microcontroller challenges, it is crucial to have a comprehensive understanding of the underlying hardware and software components. Microcontrollers are complex devices, consisting of various integrated circuits that work together in harmony. When facing challenges, it is important to analyze both the hardware and software aspects of the microcontroller system.
On the hardware side, common challenges may include faulty connections, power supply issues, or malfunctioning components. A thorough examination of the circuitry and peripheral devices can help identify and resolve these problems.
Software challenges typically involve issues such as code errors, incorrect configuration settings, or compatibility problems with other software modules. Debugging tools and techniques like breakpoints, trace features, or logic analyzers can aid in pinpointing and rectifying these issues.
Frequently Asked Questions
What Are the Most Common Hardware Limitations Faced When Working With Microcontrollers?
The most common hardware limitations faced when working with microcontrollers include limited memory, low processing power, and a lack of input/output pins. These constraints can make it challenging to implement complex algorithms or connect multiple devices.
How Can Software Complexities Be Effectively Managed and Navigated When Developing for Microcontrollers?
Software complexities can be effectively managed and navigated when developing for microcontrollers by adopting a systematic approach. This includes utilizing efficient programming languages, optimizing code, implementing modular designs, and using debugging tools for troubleshooting and resolving software issues.
What Are Some Common Design Constraints That Need to Be Considered When Working With Microcontrollers?
Common design constraints that need to be considered when working with microcontrollers include limited memory and processing power, restricted input/output capabilities, power consumption limitations, and compatibility with specific communication protocols.
Strategies to optimize the performance and efficiency of microcontroller systems include carefully selecting the hardware components, optimizing software algorithms, minimizing power consumption, and utilizing advanced techniques such as parallel processing and code optimization.
How Can Security Vulnerabilities Be Identified and Addressed in Microcontroller-Based Projects?
Security vulnerabilities in microcontroller-based projects can be identified and addressed by conducting thorough security assessments, implementing secure coding practices, utilizing encryption and authentication mechanisms, regularly updating firmware and software, and staying informed about emerging threats and mitigation techniques.

 Basic Electronics ConceptsEssential ToolsCircuit Design BasicsMicrocontrollersDIY Electronics ProjectsRoboticsPrivacy PolicyTerms And Conditions
Basic Electronics ConceptsEssential ToolsCircuit Design BasicsMicrocontrollersDIY Electronics ProjectsRoboticsPrivacy PolicyTerms And Conditions
